Leave us your email address and be the first to receive a notification when Robin posts a new blog.
Reading through the NSX-T 3.2 release notes you can instantly see that this major release includes many new features. When looking at the configmax site, you can see this is more a feature release then an increase of capacity, since most of the maximum numbers stayed the same. I’ll start with the most important features related to the Distributed firewall and go from there.
Distributed Firewall for VDS Switchports
This new feature provides the ability to extend microsegmentation to workloads deployed on vSphere networks. Before NSX-T version 3.2, a VM needed to be connected to NSX-T logical segment, for the Distributed Firewall to work. This limited the options for a virtual switch to an N-VDS or VDS version 7. With this new feature it is possible to add the Distributed Firewall to distributed portgroups on a virtual switch, starting from version 6.6 or later. Check out this blog for more details on this feature.
Distributed Firewall workflows in vCenter (NSX-T plugin for vCenter)
For small- to medium sized companies it is now possible to use NSX-T as a plugin for vCenter. Similar to how NSX-V was configured through vCenter, NSX-T can now be operated in the same manner. This can be useful for companies only requiring a subset of the features available in NSX-T, like the Distributed Firewall or other security features. In this blog you can find more details on this feature.
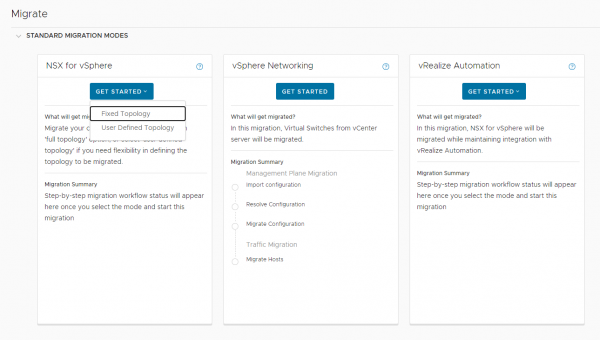
Improved NSX for vSphere to NSX-T Migration
Just before the End-General Support of NSX-V (NSX for vSphere), NSX-T brings some major enhancements to the Migration Coordinator. For example, OSPF is now supported by the migration coordinator. NSX-T 3.2 also includes the option to migrate with a User Defined Topology allowing for more flexibility in migrating from NSX-V to NSX-T.
Gateway Security
With NSX-T 3.2 the Edge or gateway firewall gets a more prominent place in the datacenter and cloud implementations of NSX-T. Where the Distributed Firewall is positioned to control the East-West traffic, the Gateway firewall focusses on securing ingress and egress traffic into and out of a zone. For example, Malware Detection and Sandboxing based on the integration with Lastline. This release includes some improvements like URL filtering and on the User-ID firewalling. Some features like TLS Inspection and Intrusion Detection and Prevention in the Gateway Firewall are only available in Tech Preview.
Distributed Advanced Threat Prevention
NSX-T 3.2 builds on the IDS and IPS features already available in NSX-T 3.1. The IDS/IPS functionality can now be deployed to a VM connected to distributed portgroups, as with the distributed firewall. The improvements to the IDS/IPS solution include more signature sources, detection mechanisms, severities, event details and update frequencies.
And much more
As said this list of improvements and new features on this major release of NSX-T is too long to discuss in a single blog. Since there are also improvements on Federation, Container Networking and Security, Guest Introspection, Load Balancing and a brand new NSX Application Platform.
Watch this website for future blog articles regarding NSX-T or check these resources to get an overview of the new features and improvements in version 3.2.
Questions, Remarks & Comments
If you have any questions and need more clarification, we are more than happy to dig deeper. Any comments are also appreciated. You can either post it online or send it directly to the author, it’s your choice.





 LinkedIn
LinkedIn
 Twitter
Twitter